Introduction
For a long time I have struggled with (the idea of) password management. Remembering unique strong passwords is impossible when one has more than a handful, which only leaves the option of using a password management system of some sort. The conventional backed-up randomly generated passwords never appealed to me, as it gets increasingly difficult to update your database of passwords with every back-up copy—and I would demand a lot of them (I refuse to ever lose my passwords).
Naturally I became interested in deterministic password-generation algorithms and I carelessly and stubbornly searched for an answer, to no avail. Time passed, and as I—on an unrelated journey—got familiar with the crypto-currency technology, the final puzzle started to fall into place. I formulated a password generator that doesn't need any back-ups, but it has not been scrutinized by anyone, let alone security experts. Hence, this is my plea and question to you: Is there a flaw or are we ready to revolutionize password management?
I will present the idea in two parts. Firstly, an explanation of the crucial obfuscation process—the final piece of the puzzle— that was inspired by Bitcoin's standard to safely store keys.
Part one: the obfuscation process
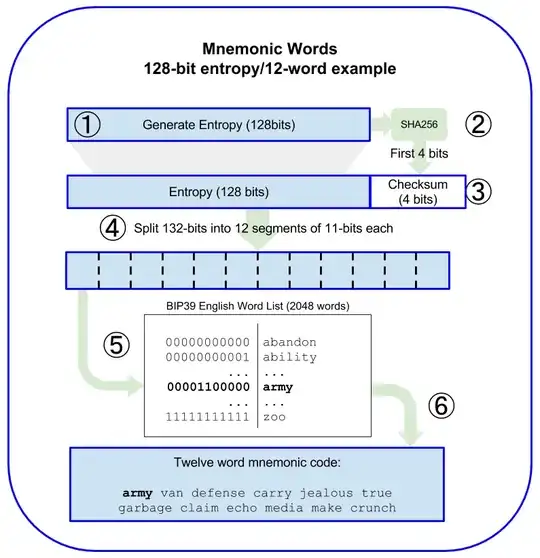
This wordlist of 2048 words is widely used in the crypto-currency space. It is used by taking a hash, appending to it a checksum sliced to the length of [entropy/32] in order to make it divisible by 11, and dividing it into segments of 11 bits—each segment corresponding to one of the words in the list (00000000000 would be the first word—"abandon", and 11111111111 would be the last word—"zoo"). Thus the hash is converted into a string of human-readable words.
Here is an infographic from Mastering Bitcoin that illustrates this:
Example:
Password:
"CorrectHorseBatteryStaple"
SHA-256 sum:
7abdae32d3c9fd31959fd66c8c48de11bdff24b1dad2542f46faa0ebc50329fe
(01111010 10111101 10101110 00110010 11010011 11001001 11111101
00110001 10010101 10011111 11010110 01101100 10001100 01001000
11011110 00010001 10111101 11111111 00100100 10110001 11011010
11010010 01010100 00101111 01000110 11111010 10100000 11101011
11000101 00000011 00101001 11111110)
SHA-256 sum with check:
7abdae32d3c9fd31959fd66c8c48de11bdff24b1dad2542f46faa0ebc50329fe5b
(01111010 10111101 10101110 00110010 11010011 11001001 11111101
00110001 10010101 10011111 11010110 01101100 10001100 01001000
11011110 00010001 10111101 11111111 00100100 10110001 11011010
11010010 01010100 00101111 01000110 11111010 10100000 11101011
11000101 00000011 00101001 11111110 01011011)
SHA-256 sum with check split into segments of 11 bits:
01111010101 (981 - "kind")11101101011 (1899 - "unhappy")10001100101 (1125 - "milk")10100111100 (1340 - "polar")10011111110 (1278 - "panic")10011000110 (1222 - "obvious")01010110011 (691 - "film")11111010110 (2006 - "wide")01101100100 (868 - "hockey")01100010010 (786 - "giraffe")00110111100 (444 - "danger")00100011011 (283 - "cash")11011111111 (1791 - "thank")10010010010 (1170 - "mutual")11000111011 (1595 - "shrug")01011010010 (722 - "focus")01010100001 (673 - "favorite")01111010001 (977 - "key")10111110101 (1525 - "salon")01000001110 (526 - "double")10111100010 (1506 - "rotate")10000001100 (1036 - "lift")10100111111 (1343 - "pond")11001011011 (1627 - "slender")
We don't need all 24 words. Taking the first 7 words we get 2048^7 > 10^23 possible passwords. That should be enough entropy.
Obfuscated password:
"KindUnhappyMilkPolarPanicObviousFilm"
This allows us to generate human-readable hashes of our passwords, which means that our passwords can be extremely similar to each other, because we will keep them secret and use their obfuscated forms instead.
Part two: the complete system
The idea is to have one strong master password for the rest of your life that works as a salt. A new password is generated by appending a name (presumably of the website) together with an integer (for multiple passwords on the same website) to the master password before it is obfuscated to create the password.
Let's assume our master password is "CorrectHorseBatteryStaple".
I wish to create a new account on StackExchange and decide to generate a password for it:
The password manager asks for a name and number (default: 1) for the password. I type
"StackExchange"and change the number to 2, as this would be my second StackExchange account.The password manager turns the name into lower case, and appends it and the number to the master password:
"CorrectHorseBatteryStaplestackexchange2"The password manager obfuscates the string and presents the obfuscated password for my new StackExchange account to me:
"ParentTinyGiftCenturyCurveBlessInput"
The password manager can save these passwords, but it is unnecessary. Whenever I want to log in to my second StackExchange account I can simply write "stackexchange" and "2" in the two fields in order to be presented with my password.
There are a few obstacles that need to be tackled. Many websites have silly restrictions on passwords such as a maximum password length of 20 and requiring non-alphanumberic characters. These problems could be bypassed by simply ending every password with an asterisk and allowing for 4-word passwords in addition to the standard 7-word password. However, I am unsure about whether it is the correct approach to include these hacks, as this should be a widely adopted standard rather than merely used by a small minority of enthusiasts.
Adoption is important to reduce fingerprintability. I am currently using this technique for my passwords, but since I am the only person on the planet who uses it, I cannot use it when I want to be anonymous. That is a major problem, but one that eventually goes away if this turns out to be as widely adopted as I think it deserves to be.
Compared to conventional password managers, this is—as I can see—more secure and incredibly more convenient (which plays a major role in adoption).
Update: I am not exactly sure why this is off-topic, but in any case I realize that my idea is infeasible after reading the comments and reflecting over them. This question may now be closed.